What a Fraudulent Insurance Claim Often Gets Wrong




Here is my hot take after a decade in fraud work: a fraudulent insurance claim usually does not fail because the fake receipt looks like a movie prop. It fails because the surrounding details are lazy.
The total is polished, but the tax is wrong. The invoice looks official, but the vendor has no normal footprint. The claimant has the perfect repair bill, but the payment trail acts like it was assembled in a hurry on a Tuesday night by someone with too much confidence and not enough bookkeeping.
That matters because claims teams are under pressure to move fast. Most false claims do not arrive wearing a villain cape. They arrive as a PDF, a phone photo, a contractor invoice, a pharmacy receipt, or a medical bill that looks ordinary enough to pass through a busy queue.
The scale is not small. The FBI estimates insurance fraud costs the United States more than $308 billion per year, adding roughly $400 to $700 to annual premiums for the average family. In 2025, BBC reporting on Admiral described a sharp rise in fraudulent claims involving AI-generated images and deepfakes. And according to Verisk’s 2025 fraud report, many carriers now see claims manipulation becoming more sophisticated.
But sophistication has a funny weakness. Fraud gets better at making the document look right. It still struggles to make the document belong to the real world.
The first thing a fraudulent insurance claim gets wrong is time
Timelines are where bad claims start sweating.
A genuine claim has a messy but explainable sequence. Loss occurs, the claimant notices, maybe calls the insurer, maybe gets emergency work, receives an invoice, pays, and submits proof. There may be gaps. There may be delays. Real life is not a flowchart, and anyone who has handled property claims after a storm knows that contractors do not appear instantly like pizza delivery.
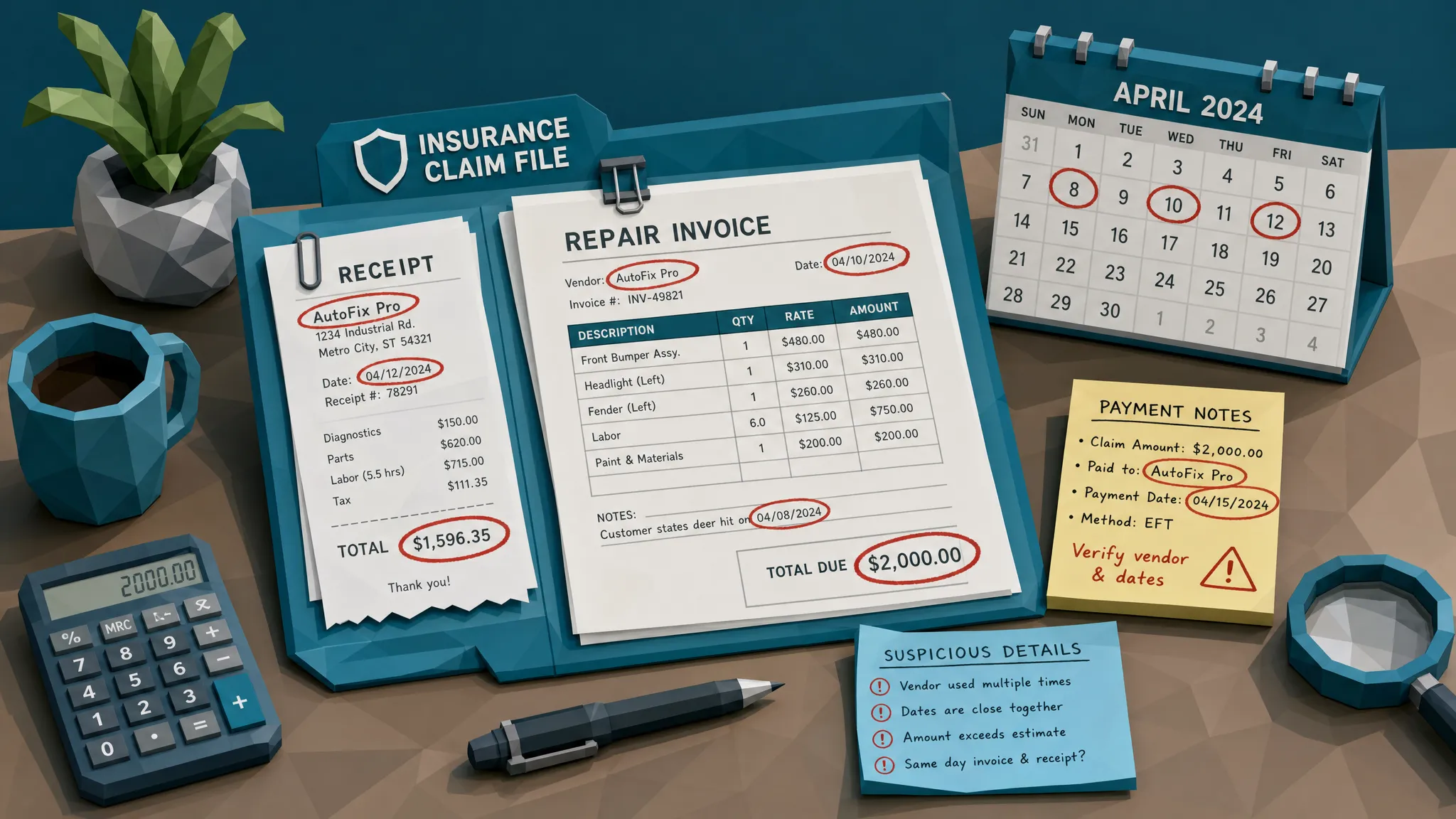
A suspicious claim often has a timeline that is either too perfect or physically awkward.
I once reviewed a water damage claim where the restoration invoice was dated before the insured had reported the leak. That alone did not prove anything. People call contractors before calling insurers all the time. But the receipt timestamp, the claimed call time, and the payment method told a different story. The “emergency” service appeared to have been paid before anyone could reasonably have known there was an emergency. The claim did not collapse because of one clue. It collapsed because the clock kept tapping us on the shoulder.
Watch for dates that cluster unnaturally, invoices produced minutes after an event, repair photos taken before the reported loss, or documents with creation dates that disagree with the claim narrative. In health insurance, the same idea applies to treatment dates, prescription fills, provider visits, and billing dates. In warranty claims, it shows up when the purchase, failure, service visit, and reimbursement request are arranged in a tidy little line that no real customer journey would follow.
My rule is simple: if the timeline reads like someone wrote it backward from the desired payout, slow down.
The payment trail is usually less convincing than the document
Fraudsters obsess over the paper. They spend far less time making the payment history believable.
That is why the payment information on a claim is so useful. A forged invoice may have the right logo, address, and line items, but the bank details may be new, the payee may not match the vendor, or the claimant may be pushing for reimbursement to an account with no sensible connection to the loss.
In a legitimate claim, payment context tends to fit the story. The card charge, bank transfer, invoice number, merchant name, and service date usually form a rough pattern. It does not have to be perfect. Real merchant descriptors are famously ugly. I have seen legitimate card statements where a roofing company showed up as something that sounded like a fishing tackle shop. Still, there is usually a thread you can pull.
A fraudulent insurance claim often breaks that thread. The claimant says they paid a local contractor, but the payment account is tied to an unrelated person. The receipt shows one merchant name, while the bank descriptor points somewhere else. The invoice asks the insurer to pay a vendor that was introduced late in the process, right before settlement. That is not always fraud, but it deserves attention.
This is also where claims teams can reduce false positives. A document-only review might flag a weird-looking receipt. A payment-aware review can ask the better question: does this document make sense given who is being paid, how they were paid, and what has happened on this claim so far?
Fake documents often look too clean
I know this sounds odd, but perfection can be suspicious.
Real invoices and receipts live hard lives. They get photographed in poor lighting, forwarded through email, scanned by office printers that should have been retired during the Obama administration, and uploaded through mobile apps with greasy fingers. Real documents have compression, shadows, folds, paper texture, uneven lighting, and sometimes a coffee stain that deserves its own line item.
Fake claim documents often overcorrect. They are crisp in the wrong places. They have perfectly flat backgrounds, suspiciously consistent spacing, or text that seems pasted into a slightly different world than the rest of the page. Digitally altered documents may show font mismatches, inconsistent baselines, cloned pixels, odd boxes around changed values, or areas with different image compression.
AI-generated receipts and invoices have improved quickly. By 2026, the obvious tells are less obvious. But generated documents still tend to struggle with boring consistency: tax labels, merchant formatting, invoice numbering conventions, street addresses, line-item spacing, and the kind of ugly administrative details that real businesses repeat out of habit.
A seasoned reviewer does not ask, “Does it look nice?” They ask, “Does it look like this specific document came from this specific vendor at this specific time?”
The math is close enough for a human skim, and that is the problem
One of the most common mistakes in fraudulent claim documents is nearly correct math.
The subtotal adds up until one line item is changed. The tax rate is right for a neighboring jurisdiction, but not the one on the invoice. A discount is applied before tax when the vendor normally applies it after tax. A contractor estimate uses plausible quantities, but the unit rates do not match the final total. A health bill includes amounts that look normal until the codes, dates, and patient responsibility are compared carefully.
This is why I do not trust “the total looks reasonable” as a control. Reasonable is how fraud gets paid.
A small example: imagine a $1,200 appliance repair receipt in a warranty claim. The line items are a $350 part, $400 labor, $80 callout fee, and $120 tax. A tired reviewer sees a normal-looking $950 subtotal and a total around $1,070 or $1,200 depending on the document. But the tax may be applied to non-taxable labor, the service fee may be duplicated, or the final total may have been edited upward after the original receipt was issued. None of that requires a criminal mastermind. It requires a PDF editor and a reviewer having a long Thursday.
The fix is not asking claims adjusters to become accountants for every document. The fix is using automated mathematical checks to identify the claims where the arithmetic does not behave like the vendor, jurisdiction, or document format suggests it should.
Vendor details are where the mask slips
Fraudulent claims often treat vendors like decorations. Real claim vendors behave like businesses.
A genuine restoration company, clinic, pharmacy, mechanic, roofer, or repair shop usually has some commercial footprint. It has recurring invoice patterns, phone numbers that answer in a normal way, addresses that make sense, licensing where required, tax identifiers, prior payment history, or at least a pattern that can be checked.
Fake or inflated claims often lean on vendors that are hard to verify. The business name may be generic. The address may be a mailbox. The phone number may be newly registered or reused across multiple suspicious claims. The invoice numbering may restart at 001 far too often. In P&C claims, I have seen “contractors” who apparently operated across three states, used the same mobile number for every trade, and invoiced with the design consistency of a ransom note. Full service, apparently.
This does not mean every small vendor is suspicious. Many legitimate tradespeople run lean operations, and some excellent local contractors have websites that look like they were built during dial-up internet. The key is proportionality. A $180 locksmith receipt needs less vendor verification than a $38,000 mitigation invoice. The bigger the payout, the more the vendor should be able to stand up to ordinary scrutiny.
When a claim may move into denial, recovery, dispute, or litigation, involve the right legal and compliance partners early. For cross-border matters or jurisdiction-specific advice, teams often work with specialized counsel or firms with international dispute experience, such as Henlin Gibson Henlin, so evidence handling does not become the weak link later.
Metadata tells the quiet version of the story
Metadata is not magic. It is not always present, and its absence is not proof of fraud. Some platforms strip it automatically. Some customers submit screenshots because that is what their phone made easy. We should not punish ordinary technology chaos.
Still, when metadata exists, it can be wonderfully blunt.
A receipt photo may show it was created weeks after the claimed purchase. A PDF may have been edited using software shortly before upload. GPS data may place the image far from the claimed repair location. A file may have a creation date that predates the invoice date, or a modification history that suggests the document went through multiple edits after issuance.
This is one reason I push claims teams to preserve original submissions whenever possible. Do not immediately flatten, resize, convert, or OCR the document and throw away the original file. Once you strip the file down to extracted fields, you may lose the very signals that explain whether the document is genuine, altered, or generated.
A practical review does not treat metadata as a judge. It treats metadata as a witness. Sometimes the witness has nothing useful to say. Sometimes the witness quietly points at the edited total and clears its throat.
Reuse is the lazy cousin of fraud
A surprising number of bad claims are not built from scratch. They are recycled.
The same receipt appears across multiple claims with a changed date. The same contractor invoice shows up with a different policyholder name. The same photo of damaged property is cropped, brightened, and resubmitted. The same medical bill template gets reused with small edits to patient details. In warranty claims, the same proof-of-purchase image may be submitted for multiple products.
Manual reviewers are terrible at spotting this across large volumes. That is not an insult. It is biology. If you handle thousands of documents a week, your brain will not remember that the smudge near the upper-right corner of a receipt also appeared in a claim from six months ago.
Systems that compare documents visually, not just by extracted text, are better suited for this. Exact duplicate checks are useful, but near-duplicate detection is where the real value sits. Fraudsters rarely resubmit the same file unchanged. They crop it, blur it, alter the total, change the date, or take a photo of a printout. The document changes costume, but the bones remain familiar.
The claimant behavior gets oddly theatrical
Documents matter, but behavior around the document matters too.
A claimant who made a genuine mistake usually helps you solve it. They send the original, clarify the vendor, explain why the receipt is a screenshot, or provide another proof of payment. Fraudulent claimants often push urgency, switch channels, resist simple verification, or provide increasingly polished but inconsistent evidence.
I have learned not to overvalue “they sounded nervous.” Claims are stressful. Honest people can sound defensive when money, property, health, or family pressure is involved. But behavior becomes useful when it lines up with document problems.
A late payee change plus a newly created invoice plus refusal to provide proof of payment is a pattern. A claimant who cannot explain why a receipt was edited after the loss date, then sends a cleaner replacement that creates a new contradiction, is giving you more than a vibe. They are giving you an escalation path.
What claims teams should do before payout
The best claims fraud programs do not rely on heroic reviewers. They build a boring, repeatable process that catches risky documents before money moves.
If I were redesigning a claims intake process tomorrow, I would keep the workflow simple. Preserve the original document. Check the timeline. Compare the document to payment and payee details. Run visual, metadata, mathematical, and duplicate checks. Route only the meaningful exceptions to SIU or senior review, with the evidence attached.
That last phrase matters: with the evidence attached. Do not send investigators vague alerts like “suspicious document.” Send them the reason. Edited total area. Conflicting timestamp. Vendor mismatch. Near-duplicate found on prior claim. Payee introduced after approval. A good alert saves time because it tells the reviewer where to look.
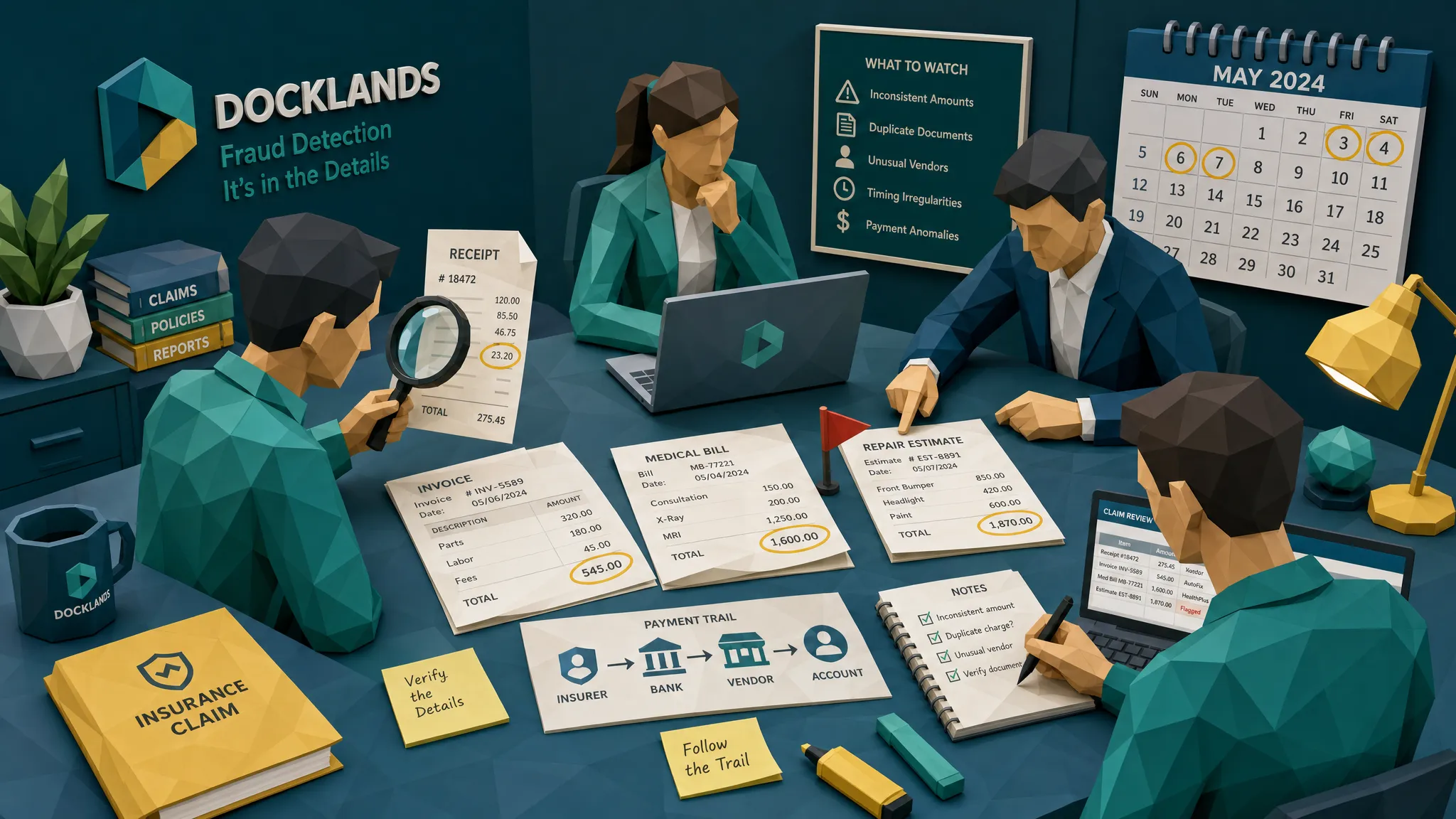
This is where Docklands AI fits into a modern claims operation. Docklands AI helps detect photoshopped, manipulated, physically altered, and AI-generated invoices and receipts. It also uses payment information around the claim, expense, or payment to build a deeper fraud picture, rather than asking whether an image “looks real” in isolation. For claims teams, that means document forensics can be connected to the payout decision before funds leave the building.
Do not turn every clue into an accusation
Here is the part I wish more fraud training emphasized: a red flag is not a conviction.
A weird timestamp might be a phone setting. Missing metadata might be a platform conversion. A messy receipt might be a legitimate photo from a claimant who has more important things to worry about than your file standards. Fraud work requires suspicion, but it also requires humility.
The goal is not to accuse faster. The goal is to sort better.
Clean claims should move quickly. Questionable claims should get a focused review. High-risk claims should be escalated with preserved evidence. That balance protects the insurer, protects honest policyholders, and gives SIU teams fewer haystacks to search.
Frequently Asked Questions
What is the most common mistake in a fraudulent insurance claim? The most common mistake is inconsistency. The document may look convincing, but the timeline, payment details, vendor information, metadata, or math often fails to match the claim story.
Can a fraudulent insurance claim be detected from a receipt alone? Sometimes, but a receipt is strongest when reviewed with context. Claims teams should compare the receipt against the payment trail, loss date, vendor history, claimant behavior, and any related documents.
Does missing metadata prove a document was manipulated? No. Metadata can be removed by phones, email systems, scanning apps, and claim portals. Missing metadata should be treated as one signal, not proof. Conflicting metadata is usually more useful than absent metadata.
Why do manual claim reviews miss altered invoices and receipts? Manual reviewers are dealing with volume, time pressure, and documents that often look normal at first glance. Subtle edits, near-duplicates, tax errors, and metadata contradictions are easy to miss without automated screening.
When should a claim be escalated to SIU? Escalation makes sense when multiple signals line up, such as an edited document, inconsistent payment details, a questionable vendor, duplicate evidence, or claimant behavior that blocks normal verification.
Catch the claim before the payout catches you
Fraudulent claims rarely get everything wrong. That is what makes them dangerous. They get enough right to look routine, then lose the plot in the details.
If your team is still relying on manual review, OCR fields, and gut feel to decide whether submitted invoices and receipts are genuine, it is time to add a stronger evidence layer. Docklands AI screens claim documents for manipulation, generated content, metadata issues, mathematical irregularities, physical tampering, duplicates, and payment-context mismatches before payout.
Because in claims fraud, the document may tell a story. The details tell the truth.
Request a Demo Today!
Book your demo below.





